“If I close my eyes, you can’t see me.”
So say young children. And so say many small to midsize businesses (SMBs) of their visibility as desirable targets to cybercriminals.
Unknown Author, CC-SA
Unfortunately, closing your eyes to your business’ cyber risk won’t protect you. This white paper addresses Cyber Risk, Readiness, and Resilience specifically for SMBs.
Just as ignoring a pesky brother doesn’t make him go away, denying your cyber risk is not an effective strategy. Most likely you WILL be attacked (or have been already and just don’t know it yet). Awareness and acknowledgment of cyber risk are the first steps to protecting your business.
The fact is, cyber risk, including crippling business interruption and financial impact from an attack, has become a leading cause of loss for SMBs. Yet it is commonly misunderstood, and is severely underestimated as a potentially fatal business risk.
Many SMBs simply lack education about the reality of the risk; others staunchly remain in willful denial.
If you have employees, you have cyber risk. If you store or manage data (whether on paper records, on an in-house server, or in the cloud); have a website; use social media; conduct e-commerce; or use a computer and the internet for other business purposes, you have cyber risk.
There are currently 10 million known cyber threats. Even the best firewalls can only protect from about 300,000 threats. Simple math. So adequate protection must combine readiness with resilience techniques.
Cyber RISK
Two major reasons SMBs are increasingly at risk are (1) a shift in cyberattack schemes, and (2) SMBs are low hanging fruit for cybercriminals.
Shift in Cyberattack Schemes
A common misconception is if you do not collect or store healthcare, financial, or other “protected” information, nor sell products online, you have no cyber risk. Yet all SMBs hold at least some protected employee or client data, and conduct online financial transactions. More important, ransomware/extortion resulting from Distributed Denial of Service (DDoS) attacks has exploded as the leading cause of loss for SMBs, for which all are at risk. Another major threat is social engineering – also known as deception fraud, impersonation schemes, or phishing.
Ransomware
Unknown Author, CC-SA
Ransomware is malicious software that locks or disables particular files or your entire computer system, until financial demands are met. Ransomware attacks doubled in number and demand amount from 2016 to 2017. Ransom demands are time sensitive and must often be paid in cryptocurrencies, for which SMBs are ill-prepared.
DDoS Attacks
Unknown Author, CC-SA
SMBs mistakenly believe they are “small fish” and not likely to hit a hacker’s radar for a ransomware attack; however, rather than manually target businesses of a specific size, cybercriminals now troll the internet with botnets that automatically identify vulnerable IP addresses. Millions of IP addresses can be identified in mere seconds to carry out DDoS attacks.
DDoS attacks have become a prominent threat because of ease of intrusion using internet connected devices as a gateway. In early DDoS attacks, hackers hijacked personal computers. When internet security experts found ways to block such attacks, hackers turned to less protected “smart” devices, or the Internet of Things (IoT). IoT devices often have much weaker security than computers and networks themselves, making their IP addresses vulnerable to hacking.
In suspense novel Steel Kiss by bestselling author Jeffrey Deaver, a serial killer turned into weapons common products with embedded electronic controls – by hacking and sabotaging an escalator; a gas stove’s pilot light; a hot water heater’s temperature control; a car’s brakes; and a table saw’s power switch. Edge-of-your seat reading.
Fiction? Yes.
Farfetched? Not at all.
This very type of sabotage was used in the 2016 cyberattack on Dyn. That incident involved tens of millions of IP addresses and caused widespread service outages in North America and Europe. It took down Twitter, Amazon, Netflix, and many other businesses, small and large. IoT devices like wearable devices, heating and cooling systems, smart appliances, automated door locks, lighting and alarm systems, and electronic toys are just some of the items turned into botnets used in cyberattacks. There are 6.4 billion IoT devices currently on the market, with 30 to 40 billion devices projected by 2020. This presents a huge risk with which identification and preventive measures simply cannot keep pace.
SMBs are Low-Hanging Fruit
SMBs are actually ideal targets for cybercriminals. Rather than being not worth a hacker’s time as many SMBs believe, they are most vulnerable to attack. They often have weak or non-existent cybersecurity, as well as fewer resources and less sophistication to manage cyber incident prevention and response. This is coupled with a false sense of complacency. Hackers seek the path of least resistance, and target businesses more easily breached than those with greater resources and stronger security.
Hackers also use automatic scanning software to easily identify weaknesses such as outdated or unpatched software, weak passwords or poor password hygiene, open web ports, or unencrypted data in transit. Once a weakness is identified, it takes mere seconds for data or funds to be stolen.
Unlike breaches of large businesses like retailer Target Corporation (which, by the way, was hacked via a third party HVAC vendor’s remote access), Home Depot and Equifax, SMBs that must close their doors permanently because of a cyber breach, an all too common scenario, rarely make the news. The lack of publicity is misleading, which is proven by insurers’ claim statistics.
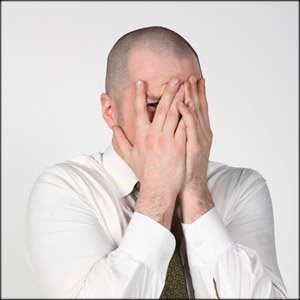
Specifically, in 2017, 31% of cyber targets were large businesses and 69% were SMBs (35% of these were small, or less than 250 employees). In 2011, 50% of cyber targets were large businesses over 2,500 employees and only 18% were small businesses less than 250 employees, according to CHUBB Insurance. This increased risk for SMBs is a steadily increasing trend.
It often takes at least four to six months from the date of a breach for a business to realize it has been breached. Some breaches are ongoing for days, weeks or months. The more time that lapses, the more expensive the incident will be to the business.
Cyber incidents result in costs such as business interruption, third party notification and credit and identity monitoring costs, forensic expense, fines and penalties, ransom or extortion payments, e-theft, reputation damage and more. Cyber insurance can cover these expenses.
Insurer claims data finds average incident costs for small firms with less than 100 employees are $60,000 to $100,000. Average costs for SMBs are $230,000 to $430,000. In comparison, Cyber insurance premiums, which include valuable resources and third-party expert services, can be as low as $1,500 to $2,000. Can your business afford not to be protected?
Cyber READINESS
A 2018 Cyber Readiness Report by insurer Hiscox reported in the aftermath of the 2017 WannaCry ransomware attack ($4 billion loss affecting 150 countries), NotPetya virus (state-sponsored malware designed to disrupt business), and Equifax breach (one of the world’s largest credit agencies), cybersecurity issues continue to escalate. Hiscox’s survey found cyber readiness shortcomings in the majority of respondents, particularly smaller firms.
What steps can you take to protect yourself and survive when you are attacked?
Face Reality
Unknown Author, CC-SA
First, acknowledge you are at risk no matter how well protected or “insignificant” you believe your business to be.
Your business’ systems can be compromised in the following ways:
- Physical access: laptops, smartphones, desktop computers, tablets, and removable media like USB storage devices
- Deliberate act by rogue or disgruntled employee
- Distribution of your legitimate username and password combinations or other confidential data on the Dark Web, where transactions of illicit and illegal services, expertise, and “products” such as personal or medical data are a booming business – cybercriminals can subcontract without disclosing identities or locations.
- Loss of service – either intentional DDoS or non-deliberate system failure due to over-reliance on a single service provider, a natural catastrophe, or technology failure
- Malicious attacks – ransomware, social engineering, viruses and worms, e-theft and more
Cyberattack victims can suffer severe reputational and financial harm, including a loss of customers and business partners. This can prove fatal for SMBs, as can the inability to operate after a ransomware attack.
Assess Your Exposure and Potential Cost of Risk
Breach of data and ransomware attacks may not be your only exposures. Many SMBs rely on Infrastructure as a Service (IaaS) and Software as a Service (SaaS) hosted off-premises, for computer applications used in daily operations and for data storage and processing, in order to reduce costs, increase capacity and efficiency, or take advantage of IT expertise not available in-house. Cloud storage is currently very vulnerable. Many SMBs mistakenly believe they are protected or held harmless if they outsource data handling or storage to a third party provider. However, SMBs could still be held responsible or suffer economic loss if that data or system is breached.
Cyber risk is often thought of in terms of liability, or financial obligations to others. However, first party risks have emerged as a key area of risk for SMBs. First-party risks encompass loss of digital assets, consequential loss of tangible assets, business interruption and extra expense, reputational harm, ransom or extortion payments. And loss of money, securities, or other property from social engineering scams.
Operating in a connected world presents unique perils which are challenging if not impossible to counteract. Cybercriminals have become so savvy, and breaches so prevalent and severe, prevention of all attacks is not realistic. While cybersecurity remains vitally important, the risk management industry focus has shifted to cyber resilience.
Cyber RESILIENCE
TheDigitalArtist, Pixabay
Implement and Monitor Protective Measures
It is clichéd, but an ounce of prevention is worth a pound of cure. A multi-faceted and holistic approach is needed to stave off and survive cyberattacks.
Government agencies will review an organization’s cyber readiness and training protocols when deciding whether to assess fines and penalties. Therefore, simply being compliant with regulations can result in a better outcome when you are breached.
Proactive steps you should take for cyber recovery include:
- Assess and remediate existing vulnerabilities and threats
- Restrict access to sensitive data, encrypt transmitted data, and avoid public Wi-Fi
- Maintain an inventory of devices and software, install security software, and replace outdated hardware and operating systems
- Keep up to date antivirus and other security software and firewalls
- Be vigilant for abnormal activity on your network
- Develop a clearly defined cyber strategy tailored to your business’ operations and personnel
- Conduct staff training including social engineering situational testing to gauge employee preparedness, and target remedial training accordingly
- Implement and routinely review and update internal cybersecurity policies and procedures – as an added benefit, formal written, enforced procedures can help protect a business from fines and penalties and claims of negligence in the event of a breach
- Develop and enforce a formal, written password policy requiring strong passwords (using letters, numbers and symbols) that are frequently changed and disabled when access is no longer needed, such as for former employees
- Achieve and maintain regulatory compliance
- Improve incident response capabilities, and respond quickly to known or suspected cyber incidents
- Comply with security requirements of business partners, vendors, and clients, and ensure third parties comply with your security requirements
- Create a Cyber Incident Response Plan, similar to other emergency response plans
Procure Cyber Insurance
SMBs often have limited (or NO) expertise, and limited resources, to handle a cyberattack. They find it harder than large firms to recover, resume operations and rebuild their reputations than larger firms. Cyber insurance can offer the necessary funding and expertise that SMBs lack.
Based on hourly costs of pre- and post-breach professional services, insurers estimate that services included with insurance policies, at no additional cost to policyholders, are worth on average $12,000 to $25,000.
- The cost of Cyber insurance might be surprisingly affordable, as low as $1,500-$2,000 for a small firm.
- An SMB that is attacked is probably experiencing a breach for the first time, while its Cyber insurer and supporting vendors are knowledgeable and experienced, and can help the business recover and make sure it stays legally compliant.
- In addition to actual defense and indemnification coverage, Cyber insurance typically includes built-in resources and experts at no additional charge, such as:
- Employee training
- Policies and procedures, including Best Practices
- Risk and vulnerability assessments, including remote system scans
- Preventive hardware/software
- Up-to-date threat intelligence and industry benchmarking
- Consultation hotlines and Incident Response Coaches – qualified experts to assist with initial event triage of an event, investigate the legitimacy and impact of an event, connect with appropriate experts, manage legalities and regulatory compliance, and coordinate an appropriate response
- Forensics experts to investigate what happened and how; and the extent of impact
- Legal experts
- Public Relations and Reputation Management experts
Additional fee-based services are typically also available
- Some of the most significant costs related to a cyber incident are Forensic, Legal, and Public Relations expenses – therefore, these are some of the greatest value-add services included with Cyber insurance policies
- The above mentioned “free” services can be leveraged to meet government compliance with respect to eLearning, vulnerability assessments, reporting, etc., saving dollars insureds would otherwise spend for compliance services (Note: GDPR, General Data Protection Regulation Compliance was recently implemented for European businesses, and may be headed soon to the U.S.)
- Some Cyber policies are now written to cover human error and/or systems failure in addition to costs for malicious incidents
Seek a Trusted Advisor’s Expertise
Unknown Author, CC-SA
Cyber insurance policy forms vary amongst insurers, and should be carefully reviewed to select the coverage best suited for your needs. It is also important to consider an insurer’s reputation for claims handling and settlement, and the value-added resources it offers. Purchase decisions made solely on the basis of price might ultimately prove more costly.
It is important to work with a knowledgeable consultative risk advisor who can assist you in obtaining the best coverage tailored to your unique risk.
To learn more about Cyber Risk, Readiness and Resilience, contact Rue Insurance: info@rueinsurance.com or 609-586-7474.